How we Security Test Mobile Applications
Our mobile application security tests include a comprehensive set of tests that evaluate the security strength of the app on the device and the app service APIs.
Sensitive information on mobile devices: We check the mobile device to see if it has adequate security measures to protect sensitive information in case the device with the app is lost or stolen.
API security: We detect any unauthorized data access using the APIs that the mobile device uses and verify that the communication between the device and the service is secure.
Sensitive information in app diagnostics log data: We review the crash reporting and app diagnostics services to find any personal or sensitive data that could be exposed in the diagnostics data, which could breach GDPR and other data protection laws.
App permissions: We inspect the device components that the app accesses and assess whether they are appropriate, such as camera, microphone, and clipboard.”
The following areas are included in mobile security testing:
- OWASP Mobile Top Ten checked
- Authentication and session implementation
- Static analysis of the application binary
- Jailbreak detection
- Broken access control
- SSL pinning countermeasure
- Testing the APIs for injection
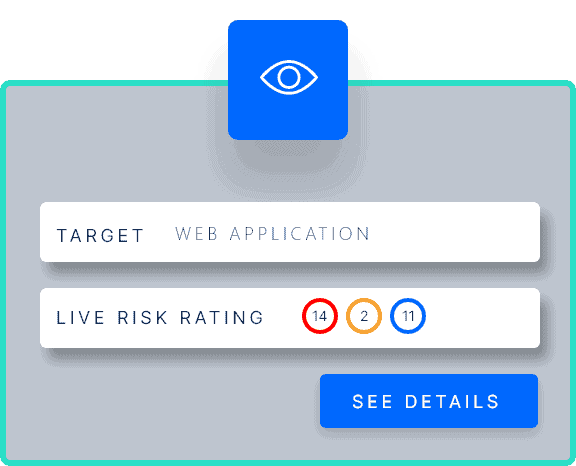
Each testing phase builds upon the other that results in the full attack surface of the web application and gives you the information that you need to action and reduce your security risk:
- API and app mapping and analysis
- Attack vector discovery
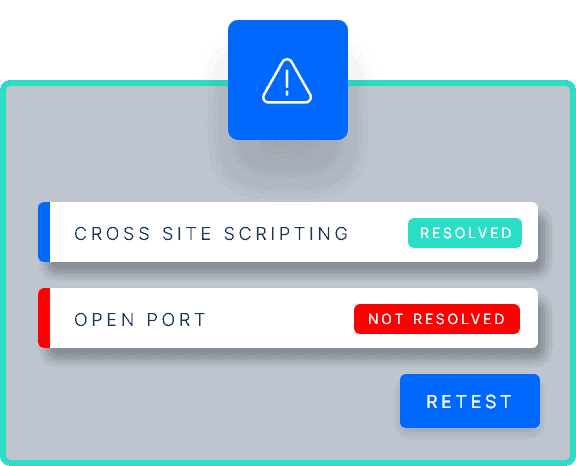
- Vulnerability identification and exploitation
Successful mobile application security testing requires understanding the whole app’s functionality and touchpoints from both an unauthenticated and an authenticated point of view.
We go further than the OWASP and recommend defence-in-depth security strategies so that you can fortify the application if a vulnerability was added.
Comprehensive dynamic security testing with different user levels allows us to see and test more of the application. This approach lets us access diverse functionality that could have various vulnerabilities that expose sensitive information