What is a continuous penetration testing service?
Our team of pentest experts will use a variety of manual and automated tools and techniques to simulate real-world attacks and identify any vulnerabilities.
We provide detailed reports on our findings, along with recommendations for remediation to help you strengthen your defences. Combining our advanced asset discovery, vulnerability scanning and expert penetration testing capability, we hunt for vulnerabilities before attackers can find them.
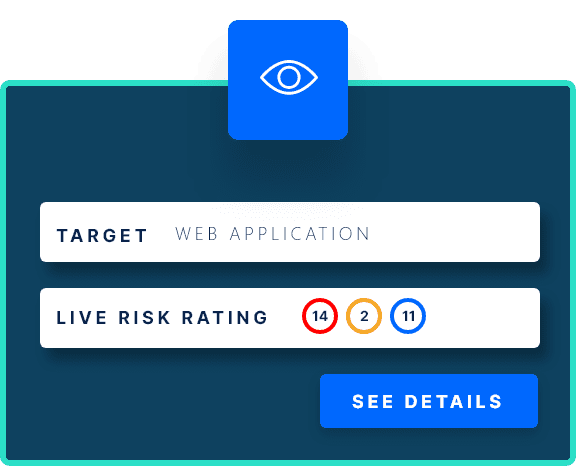
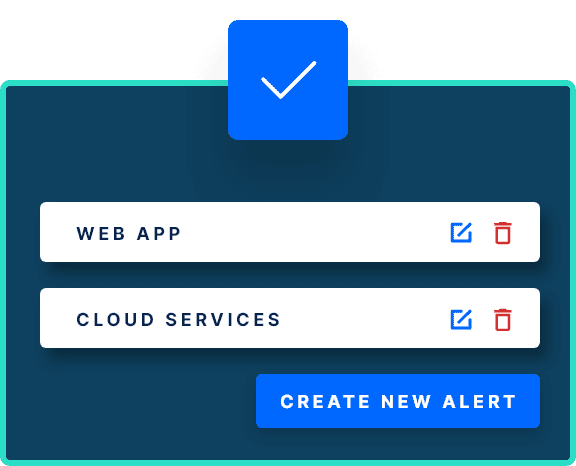
In addition to regular testing, our continuous penetration testing service also includes ongoing monitoring and alerting to help you stay informed of any potential security issues.
This allows you to proactively address vulnerabilities and keep your organization’s data and assets safe from potential threats. With our continuous penetration testing service, you can move beyond point-in-time penetration tests as part of your proactive security program.
How our continuous penetration testing service works
Our continuous penetration testing service provides ongoing and regular security assessments of your security posture. This type of security testing goes beyond traditional one-time penetration tests by providing ongoing assessments and monitoring of your organization’s infrastructure and applications. This helps to identify vulnerabilities and weaknesses in real-time, allowing you to quickly address and fix any security issues before they can be exploited by attackers.
Asset Discovery & Vulnerability Scanning
We start with the initial asset discovery process to identify and catalogue the various components of your web application such as IPs and APIs. Once the asset discovery phases has been completed we conduct vulnerability scans, port scans, and other types of automated security testing to identify weaknesses and vulnerabilities that may exist within the web application.
Baseline Manual Penetration Test
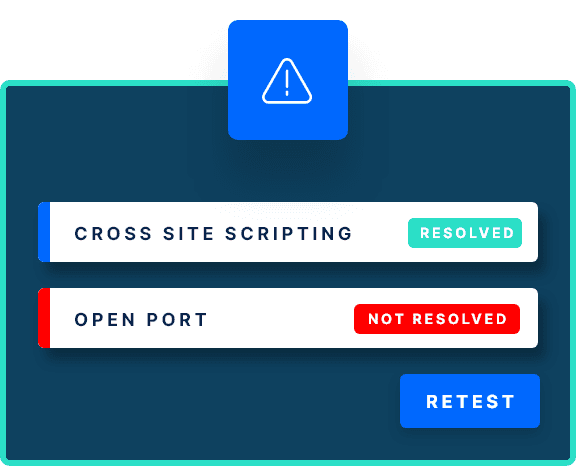
A baseline manual penetration involves manually testing the security of your web app by simulating the actions of a threat actor. The penetration test identifies and details the exploitable vulnerabilities discovered compiled in a insightful report which includes severity ratings, description, evidence and remediation advice.
Dynamic Jira Integration
Vulnerability findings from the baseline test are sent to your designated Jira project enabling your development team to start on remediation. Each ticket includes all the details found in your baseline test report meaning they don’t have to log into the Informer platform to start securing your attack surface.
Risk-Based Vulnerability Prioritization
Prioritize remediation using CVSS severity ratings to address your critical security issues first. This approach allows organizations to prioritize their resources and focus their efforts on addressing the vulnerabilities that pose the greatest risks.
Iterative Ongoing Penetration Testing
We perform ongoing penetration testing of any new features, code changes to an existing feature and updates to underlying infrastructure. The two way Jira integration means you create tickets on your Jira project which automatically creates the scope for each new penetration test.
The benefits of a continuous penetration testing service
There are several core benefits to our continuous penetration testing service, including:
Improved security
By regularly penetration testing the security of your web applications, APIs, and infrastructure you can identify and address vulnerabilities before attackers can exploit them. This can help prevent data breaches and other security incidents.
Early detection of vulnerabilities
Identify vulnerabilities early on in the SDLC before they are deployed to production . This gives you the opportunity to fix the vulnerabilities and help to upskill developers on secure coding best practice.
Reduced risk
Moving beyond traditional penetration testing vastly increases the breadth, depth and frequency of your penetration program. This can helps to reduce risk, protect your reputation and avoid costly disruptions to your business.
Compliance
In some industries, continuous penetration testing is required to comply with regulations and standards. By conducting regular tests, you can ensure that your organization remains compliant and avoid potential fines or penalties.
Improved response time
Improve your organization’s capabilities to address identified vulnerabilities. By accessing pen testing vulnerabilities as they are discovered you can increase your mean time to detect (MTTD) and mean time to remediate (MTTR).