Our Approach to External Network Penetration Testing
We use a combination of automation and manual network penetration testing to quickly detect any vulnerabilities that result from misconfiguration in operating systems or open network services that could be used to gain unauthorized access to the network or key servers from the internet. We test web servers, VPNs, firewalls, routers, mail servers, and various networking services.
To provide you with a high level of confidence, our testers use a detailed methodology and their expertise to discover a variety of vulnerabilities.
What are the three types of penetration testing?
Several approaches can be taken to testing depending on the assurance that you need.
Black Box Testing
We only work with the IP address, IP range, or domain name that you give us, and we evaluate an environment as an external hacker who has no knowledge of the infrastructure.
Grey Box Testing
We get some information about the environment to help us make better decisions about how to test the system.
White Box Testing
We use network diagrams and technical information to design and perform a focused and comprehensive network penetration test.
How we security test external infrastructure
Several testing stages follow that result in an effective test. By using our platform’s cyber intelligence capability together with expert penetration testing knowledge, Informer’s testers identify your true attack surface with depth.
- Asset discovery – asset mapping is using Informer’s discovery tools and intelligence engine
- Service identification – identifies live services that are accessible from the internet
- Vulnerability analysis – each service is analyzed in detail to identify misconfigurations and software vulnerabilities
- Service exploitation – exploitation will be performed to verify vulnerabilities and gain access to infrastructure
- Gain additional access & pivoting – successful exploitation will be used to gain further access to connected networks and hosts
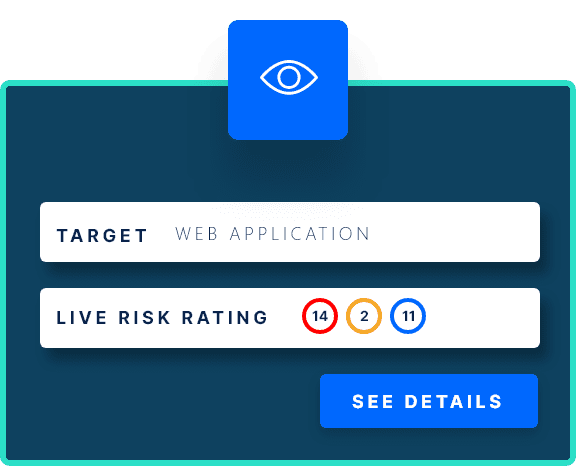
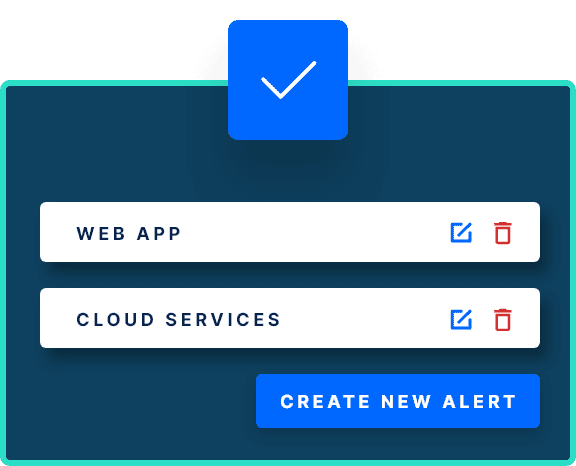
Instant online reporting
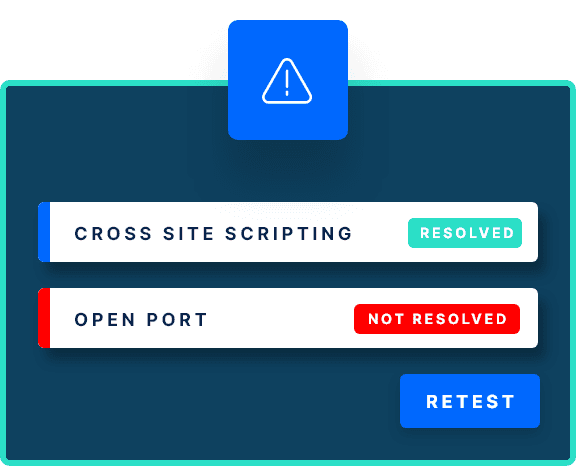
Our external network penetration testing service uses our SaaS platform to give you a quick and interactive security testing experience. You can fix vulnerabilities as soon as our testers discover them without waiting for the test to end. Use our Jira integration to create tickets automatically for your developers to resolve issues.
Each test comes with a summary that gives you a simple overview of the results. For each vulnerability discovered, you can access:
For each vulnerability discovered, Informer provides a:
- Description of the finding
- Evidence detailing the location and parameters affected
- Screenshots
- Remedial action and recommendations
- References to more information if you need to dig deeper
Each external infrastructure test is stored separately in our platform so you can access detailed findings fast or export them in a PDF report. You can download reports in a number of formats at any time during or after the test.
Technical support and debrief sessions
Our external infrastructure penetration testing service does not end with delivering reports. Our commitment extends to offering comprehensive debrief sessions with our expert penetration testing team. During these sessions, you’ll have the opportunity to discuss findings, ask questions, and seek advice. Whether you’re part of the security, IT, or development teams, we’re here to empower you with actionable insights.