Last Updated on 7 June 2023 by Alastair Digby
Table of Contents
Penetration tests are one of the most effective ways to unearth security risks in your company’s IT environment and address them before threat actors target any weaknesses. These weaknesses could include exploitable vulnerabilities in web applications, excessive access permissions, or misconfigurations, each of which could arise after changes made by system administrators or users.
No other tool or test provides the level of insight into the weaknesses exposed to real-world hackers and the opportunity to proactively strengthen your cyber security posture. However, given the frequently changing IT environments of today and the relentless emergence of new threats, pen testing frequency is a subject of continuing debate. So, how often should you penetration test? Read on to get some answers to this question that’ll help your company decide on a suitable testing frequency and how newly discovered threats should be addressed.
Why Perform a Pen Test In The First Place?
There are a plethora of increasingly advanced automated tools available to find vulnerabilities in your environment. While automated scanning definitely has its place, no tool or scanner can really replicate how penetration testing emulates real-world cyber-attacks.
Qualified ethical hackers and cyber security professionals probe your IT environment and adapt their methods on the fly to access critical systems in much the same way a motivated cybercriminal would. Some reasons to add penetration as an essential part of a holistic cyber security strategy are:
- Identify the kinds of weaknesses and vulnerabilities with the potential to cause data breaches and all their associated costs (which add up to over £3 million based on IBM’s latest figures).
- Determine if current security controls are effective and address any gaps that lead to excessive risk exposure
- Comply with regulations (like PCI DSS) that require pen testing
- Put incident response processes, teams, and plans to the test to assess their effectiveness
- Find out the level of current cyber security awareness among staff members and work to refine training materials based on identified gaps
If these reasons to perform a pen test seem like they only apply to high profile companies, think again. Small and medium-sized businesses with an Internet-exposed attack surface are also targets of malicious actors and would most definitely benefit from pen tests. Ultimately, improved security resiliency comes from the ability to think like a hacker and come to a better understanding of how to protect your systems and assets, whatever the size of your company is.
Standard Approaches to Pen Test Frequency
The first point of note is that regular penetration tests are non-negotiable. You don’t just perform a penetration test one time after going live into production and consider this activity done. Even if you take the somewhat reactive approach of considering pen tests a box to tick as part of compliance requirements rather than as a central part of your security strategy, many regulations call for regular testing.
There is no general consensus on how often you should perform penetration testing. One survey found that 85 percent of respondents pen test at least once per year while 39 percent test one to two times each year. These results reflect a common recommendation in the security community to conduct at least an annual or biannual test. But with a small minority testing as regularly as quarterly, it’s worth examining whether these businesses are a step ahead of the rest or going over the top.
What Do Compliance Requirements Say?
Annual or twice yearly pen tests are far better than never testing at all, but it’s worth diving deeper into the question of pen test frequency by taking a look at what compliance standards say.
- For businesses storing, processing, or transmitting cardholder data, PCI DSS says that companies need to pen test at least annually and upon significant changes. A significant change includes any infrastructure or application upgrades that affect access to cardholder data or the security of the cardholder data environment. The scope of these tests applies to public-facing attack surfaces and the internal cardholder data environment.
- Businesses wanting to demonstrate sufficient data protection controls through a SOC2 audit or robust information management systems with ISO 27001 can use penetration tests. Although neither of these standards specifically mandates penetration testing, ISO 27001 references ongoing improvements to information management systems.
- Article 32 of GDPR requires a process for regularly testing, assessing, and evaluating the effectiveness of technical and organisational data protection measures.
These regulations and compliance standards point toward the significant changes that occur in IT environments and to the threat landscape outside of the typical once or twice yearly penetration test.
Expanding Your Pen Test Frequency
There’s a strong argument for expanding to more regular pen tests than the once or twice per year rule of thumb commonly communicated within the security community, as the security measures in most companies often, do not prove to be as effective as believed. The crux of this argument rests on the fluidity of most modern IT environments. In the periods between annual or biannual tests, some of the following changes often occur:
- Important changes to the underlying infrastructure on which applications run, such as moving from on-premise to the cloud or switching cloud vendors
- Deploying a new application into production
- Adding new network infrastructure or switching to different hardware vendors (e.g. replacing a firewall)
- Altering end-user policies in such a way that it impacts the security of an IT system
- Strategic business adjustments, such as adding a new office location or merging with another company
Each of these significant changes carries with it a possibility of introducing new security weaknesses that could otherwise go unrecognized. Bearing in mind the cyber security risks you’ve deemed most pressing, increasing your testing frequency to reflect significant changes that might increase those risks beyond an acceptable level is a smart move. But remember, pen testing is most powerful when accompanied by insights from experienced pen testers themselves.
Obviously, other factors should come into play, including your budget, company size, and specific industry.
External Attack Surface: Continuous Testing
One overlooked aspect in the discussion is the continual bombardment of Internet-facing assets with malicious actors constantly probing those assets for weaknesses that might allow them inside your network. Motivated cyber criminals don’t stick to a once per year schedule — 65,000 hacking attempts target SMBs in the UK each day.
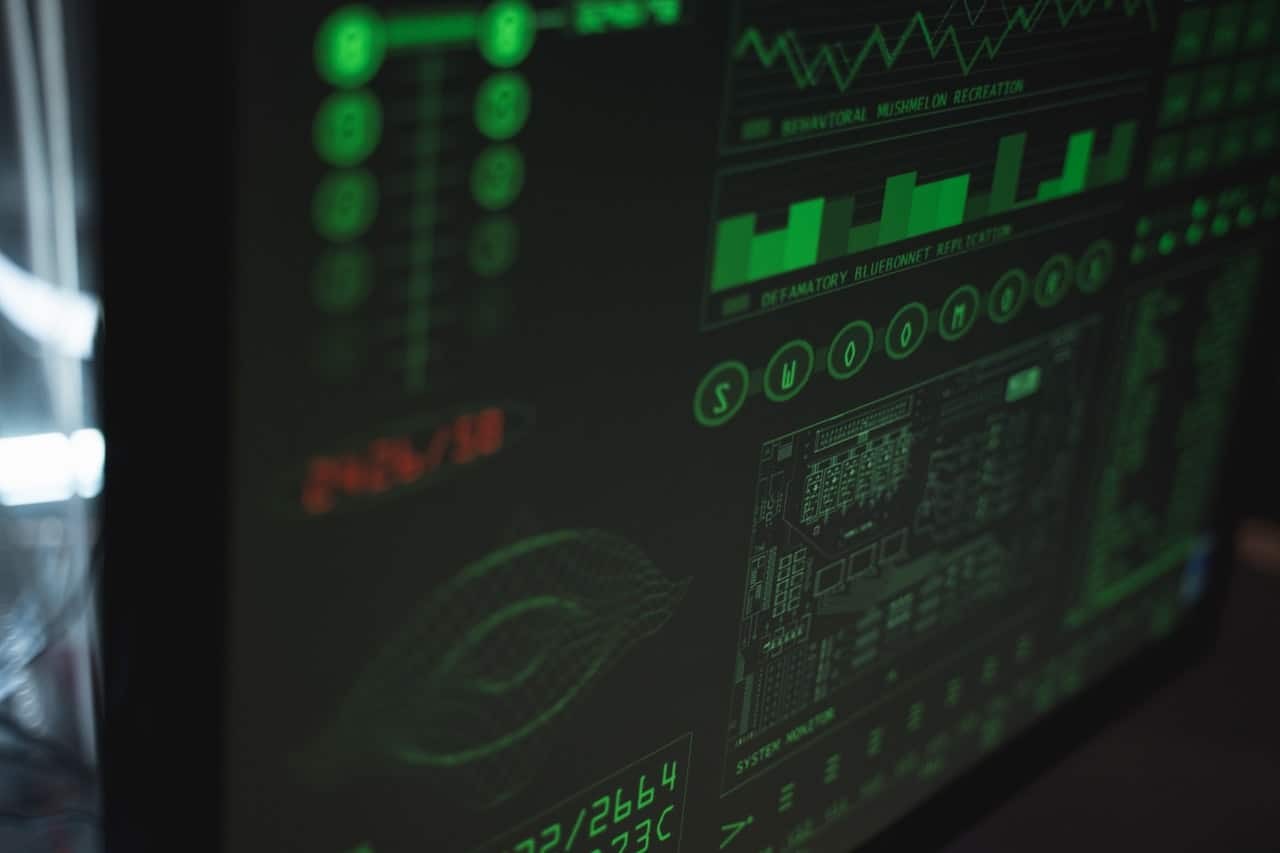
Constant change combined with an external attack surface facing persistent, evolving threats has spawned a demand for greater agility in pen testing. Continuous pen testing goes beyond standard penetration test approaches to constantly monitor your evolving external attack surface and trigger penetration tests on-demand, after any significant changes. Such an engagement better reflects real-world threat conditions and leads to faster remediation of weaknesses emerging in your environment.
Informer’s external attack surface management platform provides discovery, inventory, classification, prioritization, and security monitoring of your external assets. Integrated into the platform are penetration testing capabilities with real-time results delivered directly into the system rather than waiting around for reports.